Configuring Intune for Facilitating Device Management for G Suite Users
AUTOMATING ONBOARDING STUDENTS AND USING MICROSOFT TO MANAGE G SUITE
PART 3: CONFIGURING INTUNE FOR FACILITATING DEVICE MANAGEMENT FOR G SUITE USERS
PROBLEM
The typical IT admin in this scenario requires their School Information System (SIS) to synchronize student data their on-prem AD, Azure AD, and G-Suite. Currently, they feel that neither Microsoft nor Google has provided them with a convenient method with which to both effectively and efficiently manage the identities in these seemingly disparate environments
OBJECTIVE
By integrating Azure Active Directory with G-suite, we will be able to administratively manage an organization's on-prem AD, Azure AD, and G-suite identities from a single portal. In addition, with G-suite's identity management being delegated to Azure AD, we can redirect the SIS's synchronization from G-suite to either the on-prem AD or Azure AD.
In this way, we will have a continuous stream of data flowing from one entry point, that is reflected in all relevant directories. Such a seamless system will make the provisioning of identities, access permissions, and group memberships a simple process for IT administrators.
PART III: CONFIGURING INTUNE FOR FACILITATING DEVICE MANAGEMENT FOR G SUITE USERS
In part 3 of our blog on managing G Suite identities with Microsoft, we will be reviewing how to create an Intune Configuration Profile for easily provisioning managed devices with the appropriate Wi-Fi settings to join your network.
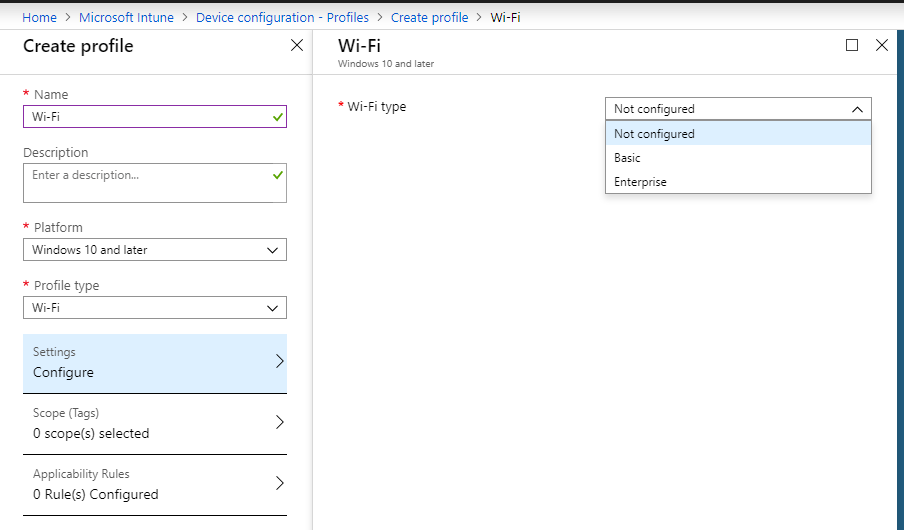
Firstly, we will name the Intune Device Configuration profile, indicate the device Platform, and select Wi-Fi as our Profile Type.
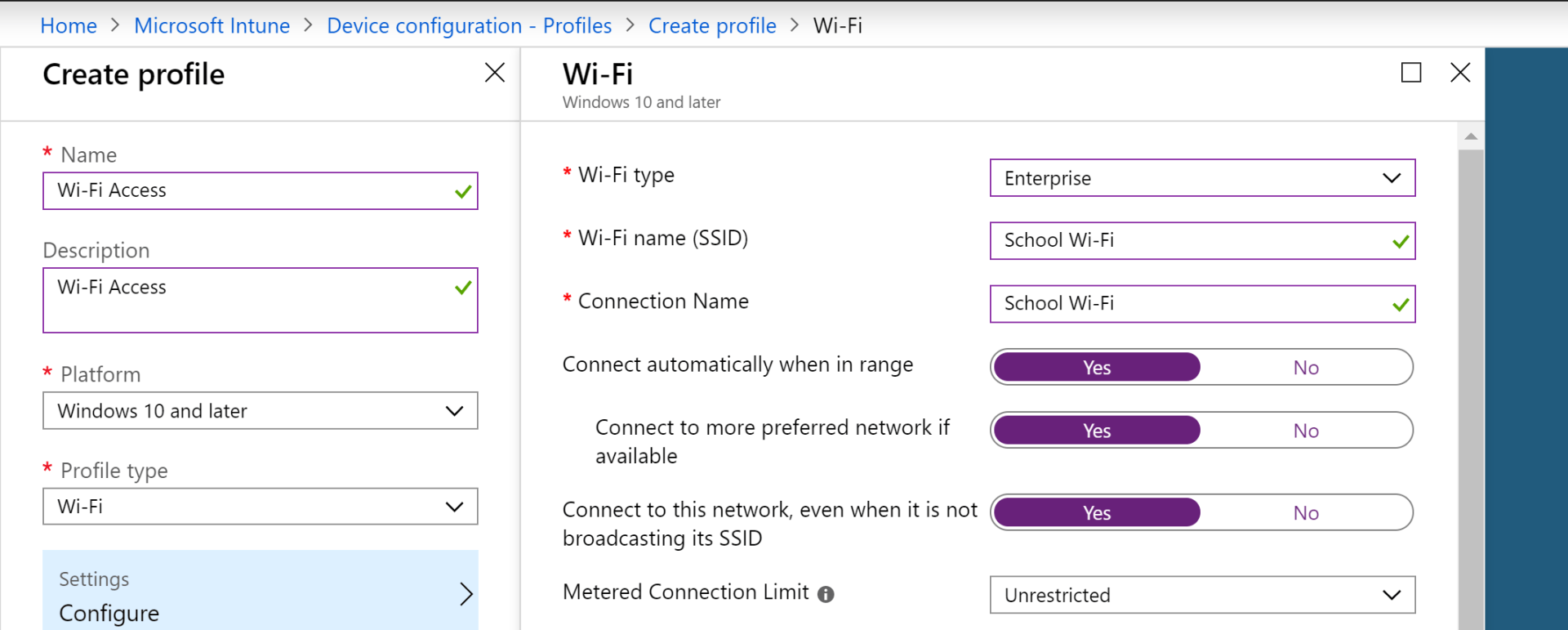
With the profile name, we can proceed with selecting our Wi-Fi type. The below screenshot is for the Enterprise selection.
In this view, we can specify the Wi-Fi name, Connection Name, fast roaming settings, and more.
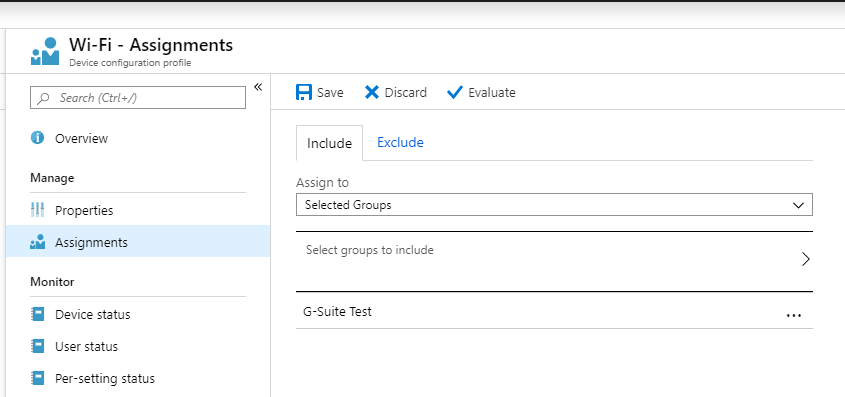
From there, we simply need to assign our group of G Suite users to the Wi-Fi policy that we just created.
There we have it. Our Intune wireless provisioning now works in conjunction with our AD-linked wireless SSID. As you can see, the benefits of integrating Azure AD with G Suite go beyond just the management of cloud identities. And since those same identities also exist in our on-prem AD, we can easily apply network access policies to them.
CREATE CONDITIONS FOR LEARNING- LEARN MORE ABOUT INTUNE FOR EDUCATION