Automating Onboarding Students Using Microsoft to Manage Google Workspace Part 1 (Configuring SSO for G Suite in Azure AD)
Part 1: Configuring SSO for G Suite in Azure AD
Problem
The typical IT admin in this scenario requires their School Information System (SIS) to synchronize student data their on-prem AD, Azure AD, and Google Workspace. Currently, they feel that neither Microsoft nor Google has provided them with a convenient method with which to both effectively and efficiently manage the identities in these seemingly disparate environments
Objective
By integrating Azure Active Directory with Google Workspace, we will be able to administratively manage an organization's on-prem AD, Azure AD, and Google Workspace identities from a single portal. In addition, with Google Workspace identity management being delegated to Azure AD, we can redirect the SIS's synchronization from Google Workspace to either the on-prem AD or Azure AD.
In this way, we will have a continuous stream of data flowing from one entry point, that is reflected in all relevant directories. Such a seamless system will make the provisioning of identities, access permissions, and group memberships a simple process for IT administrators.
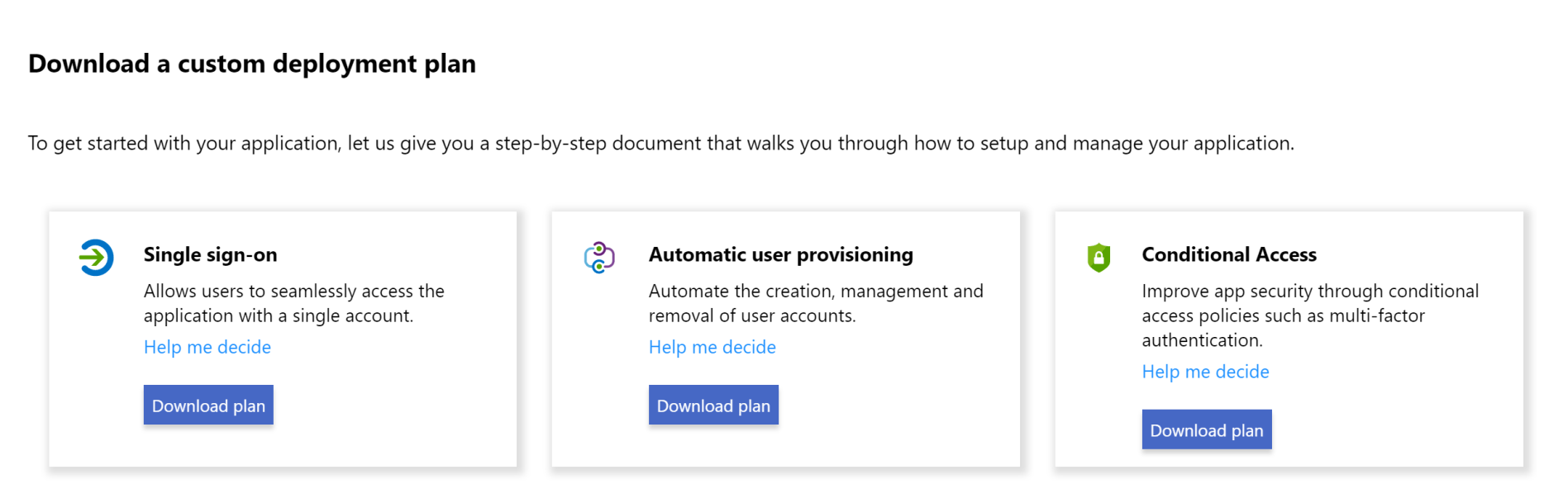
Let’s begin by reviewing the different facets of the configuration of Single Sign-On in Azure:
The 3 areas of focus for setting up SSO integration with Google Workspace for our students will include
- Configuring SSO parameters in Azure and Google Workspace
- Enabling Automatic User provisioning from Azure AD to Google Workspace
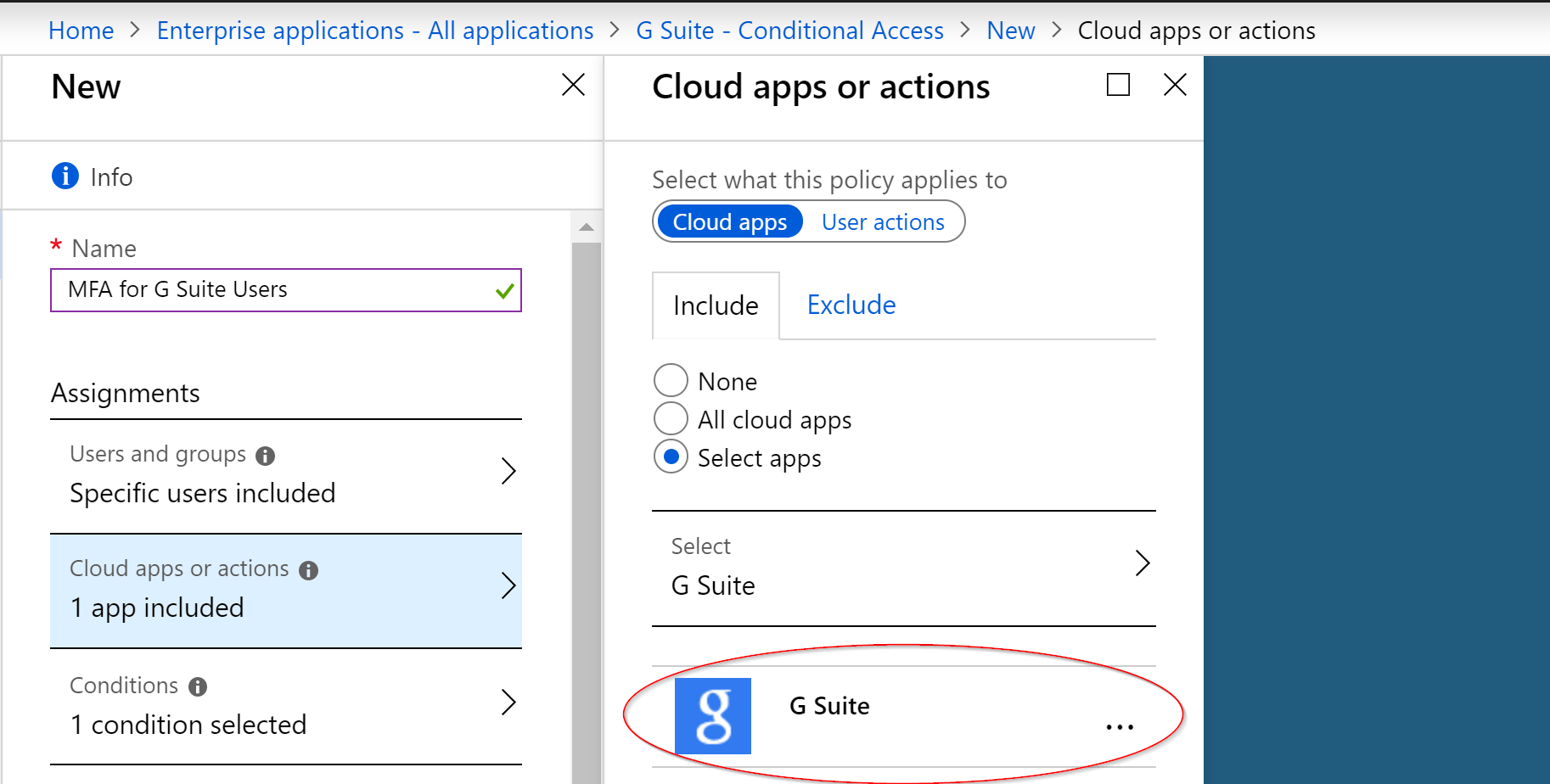
- Creating Conditional Access policies to further secure Google Workspace identities once they are tied to Azure AD identities
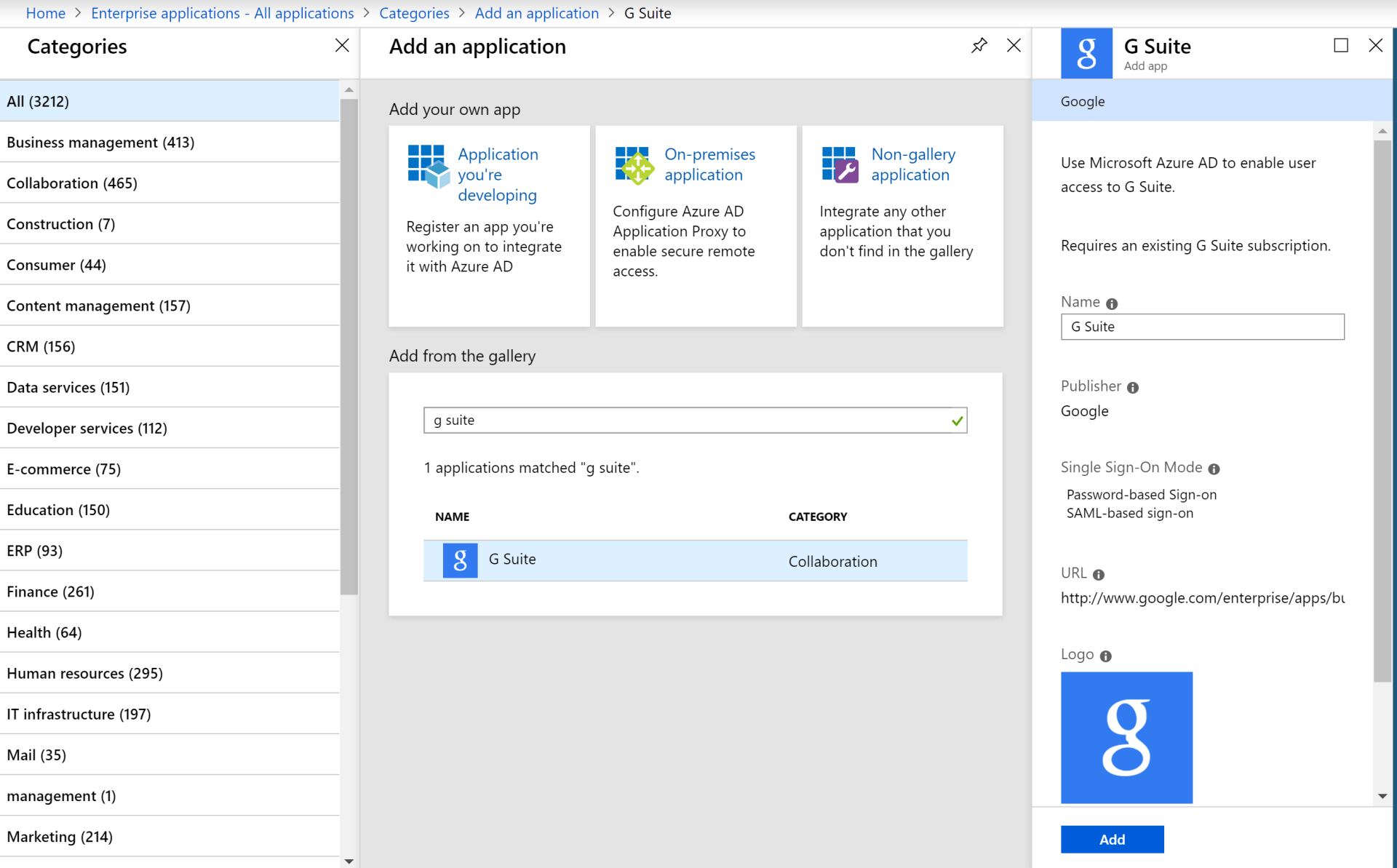
To integrate Google Workspace with Azure AD, we first need to navigate to Enterprise Applications in our Azure portal, and add Google Workspace (which will be a collective of all the apps under the Google Workspace umbrella):
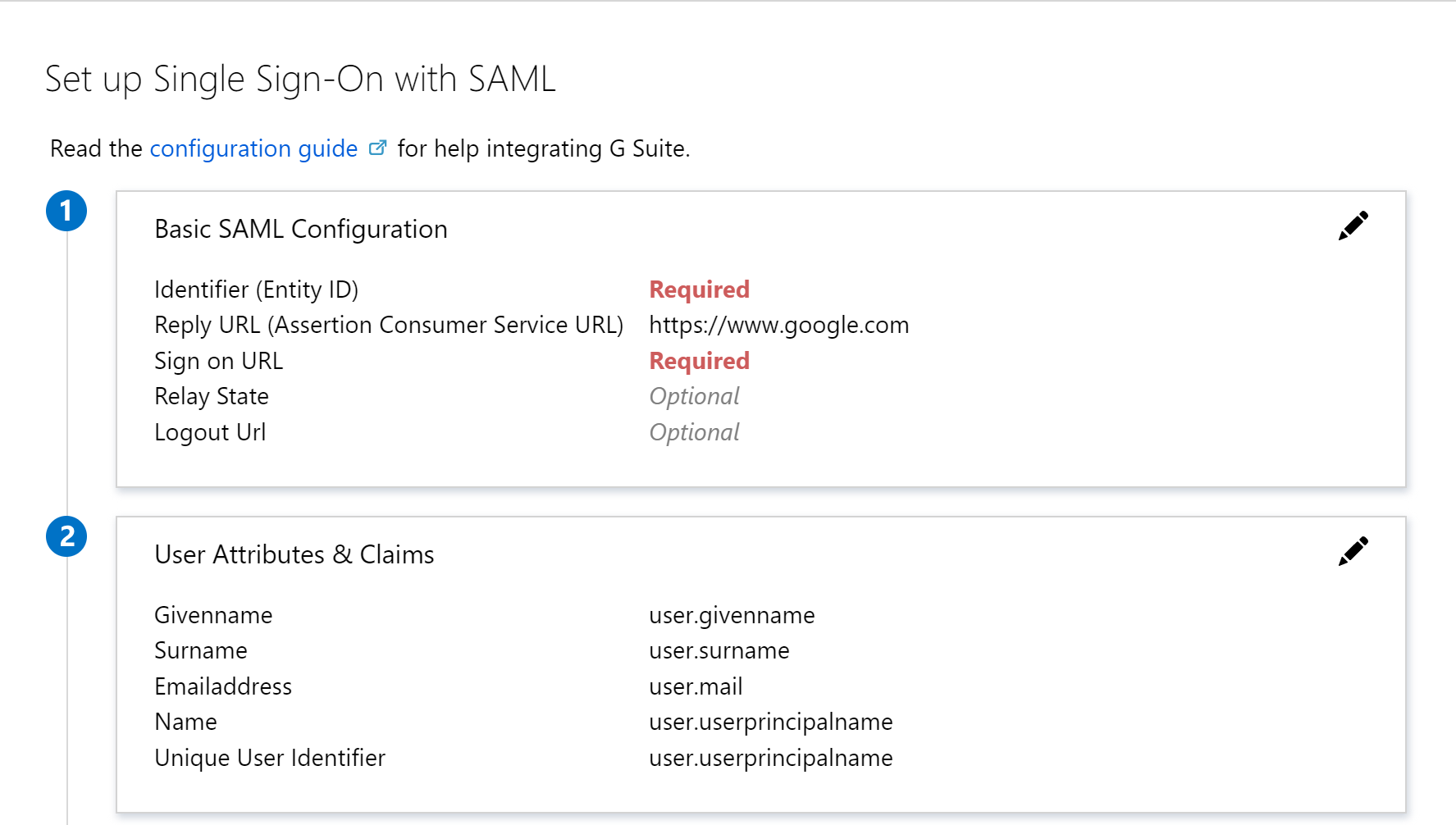
After adding the Google Workspace app platform, we will select SAML for our Single Sign-On experience, which will then provide us with the information we need to configure the SSO options in Google Workspace:
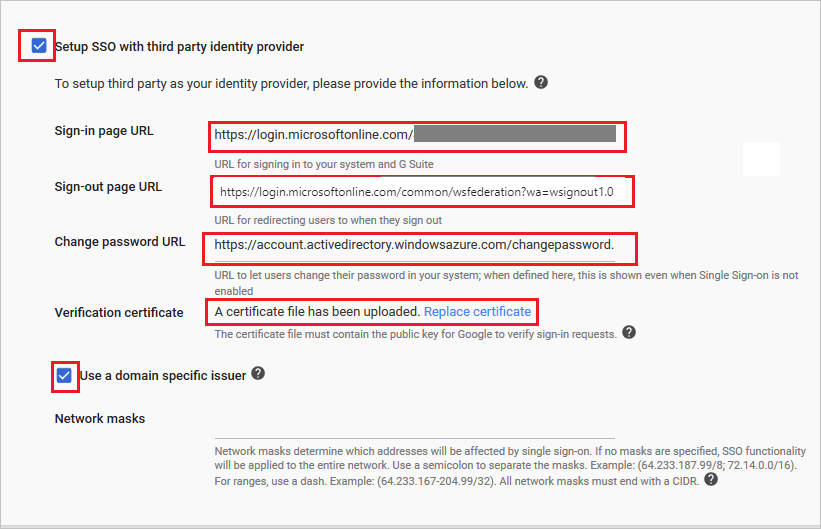
Armed with that information, we can enable SSO with third party identity providers in Google Workspace and fill out the required fields based on the information supplied to us in our respective SAML page:
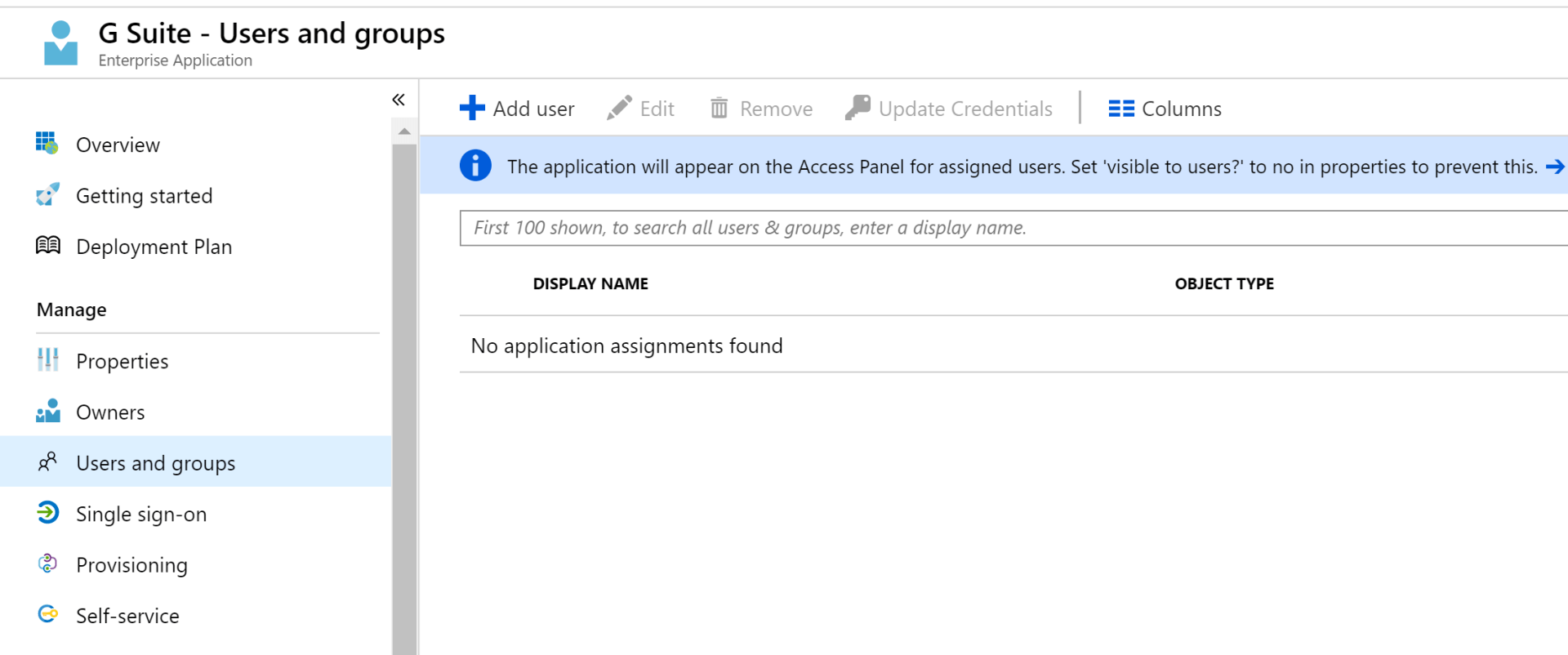
Once we have established the SSO connection between Azure and Google Workspace, we will need some users assigned to our Google Workspace app platform:
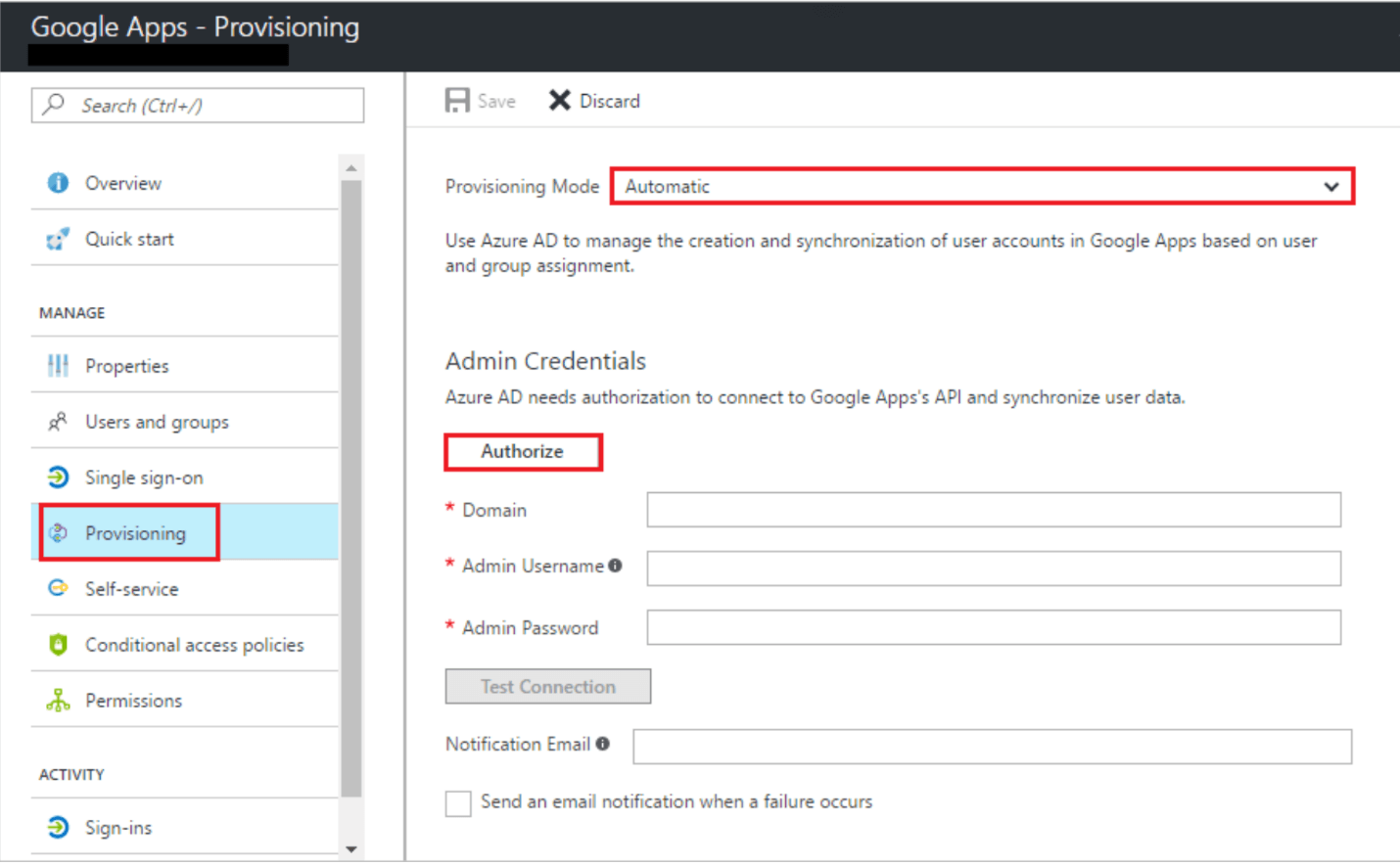
Now that we have assigned users to the G Suite app platform, let us continue into setting the Provisioning Mode to Automatic, and provide the Google admin credentials needed to authorize Azure AD to create accounts in G Suite.
And lastly, once we have integrated Azure SSO with G Suite, we can create conditional access policies that protect identities that exist in Google Workspace because they are authenticated through Azure AD during sign-in:
This concludes part 1 of our series on Automating Onboarding Students and Using Microsoft To Manage Google Workspace.