How to Hard Match Office 365 Identities to On-Premise Users
When migrating from on-premise exchange to Office 365, IT administrators can experience failure when attempting to soft match identities. Soft matching (also known as "SMTP matching") can fail for many reasons, the common one being because Office 365 detects that the email is already associated with another object. In the case of a soft match failure, a hard match must be performed. The solution to this is to stamp the online identities immutable ID with the GUID from the on-premise user, which can be done on-premise on the Active Directory server.
This is a simple PowerShell solution to hard match an on-premise GUID to an immutable ID for an online user. This ensures that all on-premise identities are correctly matched and linked to the Office 365 identities, which allows for full Office 365 write-back functionality in an organization's environment.
Provided below is the step-by-step guide on how to carry out this solution:
- Remove on-premise Identity from syncing with O365
- Remove on-premise Identity from O365 and Remove from Recycle bin
- Launch Powershell and run the following Commands
- Set-ExecutionPolicy RemoteSigned
- $credential = Get-Credential
- Input admin credentials for Office 365 and run the following command
- Import-Module MsOnline
- Connect-MsolService -Credential $credential
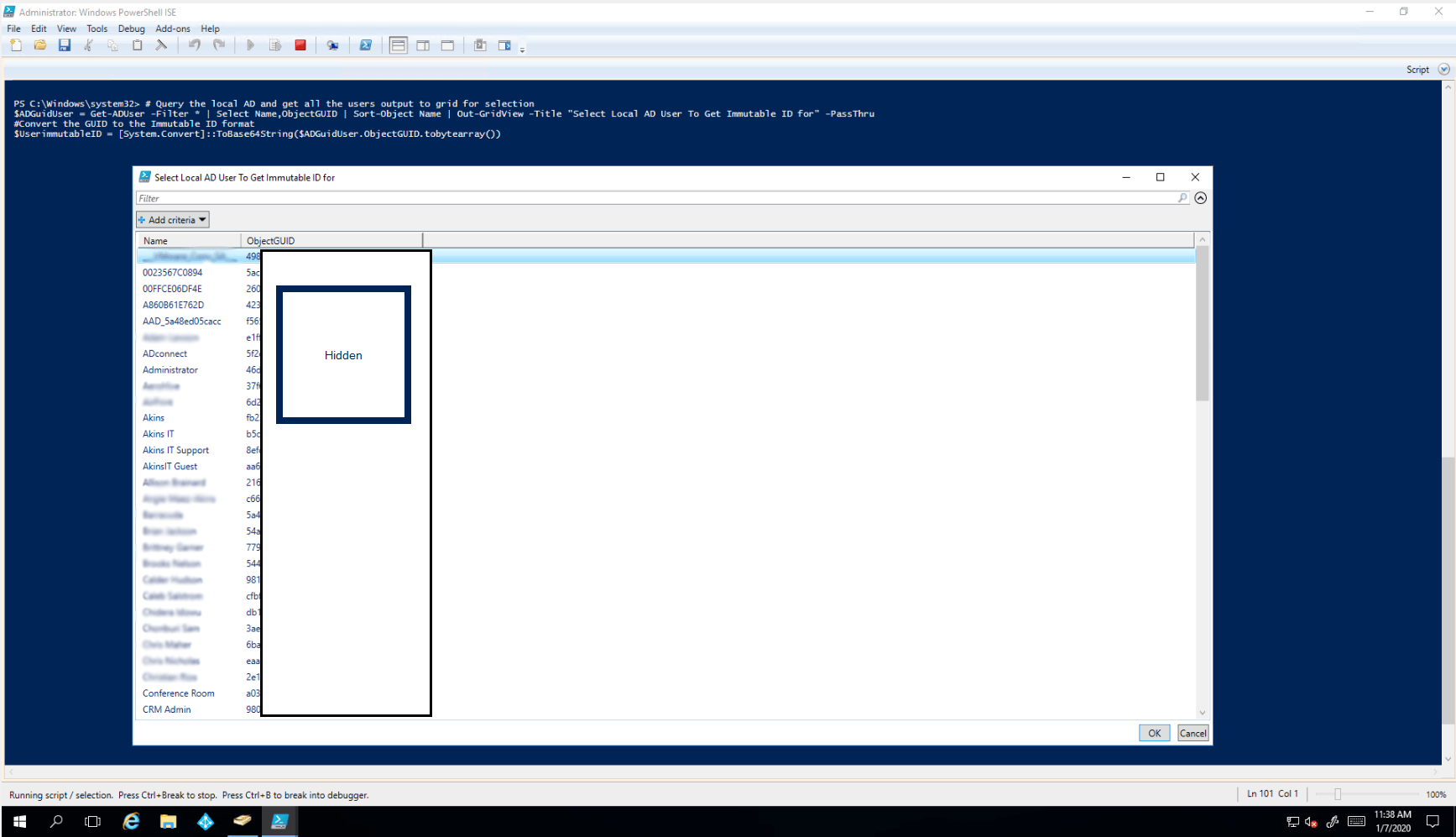
- Run “$ADGuidUser = Get-ADUser -Filter * | Select Name,ObjectGUID | Sort-Object Name | Out-GridView”
- Select the on-premise user from the Grid
- Run “$UserimmutableID = [System.Convert]::ToBase64String($ADGuidUser.ObjectGUID.tobytearray())” in powershell to convert GUID to the immutable ID format
- Run $OnlineUser = Get-MsolUser | Select UserPrincipalName,DisplayName,ProxyAddresses,ImmutableID | Sort-Object DisplayName | Out-GridView -Title "Select The Office 365 Online User To HardLink The AD User To" -PassThru”
- Select the Online identity to match on-premise identity
- Run “Set-MSOLuser -UserPrincipalName $OnlineUser.UserPrincipalName -ImmutableID $UserimmutableID”
- Set the Online identity with the new immutable ID
- Run “Set-MSOLuser -UserPrincipalName $OnlineUser.UserPrincipalName -ImmutableID $UserimmutableID”
- Check the immutable id matches
- Run the following two lines and confirm IDs Match
“Write-Host "AD Immutable ID Used" $UserimmutableID”
“Write-Host "Office365 UserLinked" $Office365UserQuery.ImmutableId”