Security at your Front Door - How to Enable Azure Active Directory Identity Protection
This security feature tends to generate many WOW moments with our clients. ID Protect is the service that assesses your login, ensures you are not breaking your normal behavior patterns, that your password is not compromised on public databases and that you aren't exhibiting signs of impossible travel. Risky logins can be re-affirmed with Multi-Factor Authentication, or an automated password reset.
The telemetry, data and intelligence is already there, enabling ID Protect simply unlocks it.
Almost universally, our clients look through the alerts after enabling and discover some immediate concerns that need action. We have had:
- A client detect that their CFO's login was compromised by a user in Russia, who was using mailbox access to send out bad mail requesting wire transfer funds. The CFO had no business relationships in Russia and had never travelled there.
- Another client find 12 of their users had leaked credentials online. We used an automatic risk based password policy to force these users to immediately change their passwords.
- Yet another client with 3000 users discover that there was a brute force campaign targeting their C-Suite.
- This is all useful information that the above environments were previously oblivious to.
Azure Active Directory Identity Protection is a new capability that provides a consolidated view into suspicious sign-in activities and potential vulnerabilities and with notifications, remediation recommendations and risk-based policies that help you protect your business.
Again, the service detects suspicious activities for end user and privileged (admin) identities based on signals like brute force attacks, leaked credentials, sign ins from unfamiliar locations, infected devices, to protect against these activities in real-time. More importantly, based on these suspicious activities, a user risk severity is computed and risk-based policies can be configured and automatically protect the identities of your organization.
Contact Akins IT to setup your trial so you can assess this insight for up to 90 days and 250 users in your environment. This is a no obligation trial and does not convert automatically to a paid subscription.
Want more info on Azure AD?
Steps to enable Azure Active Directory Identity Protection:
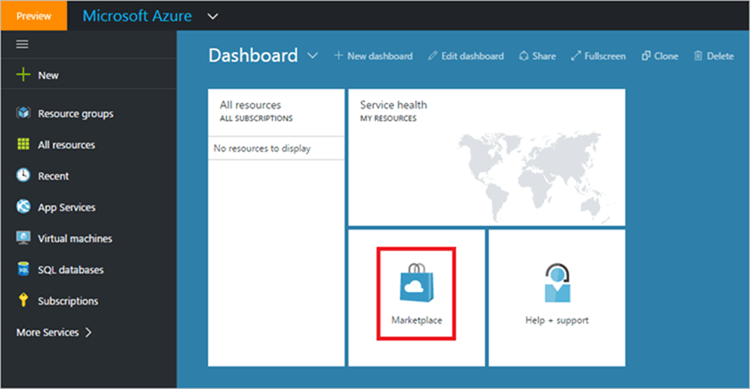
- Sign-on to your Azure portal as global administrator.
- In the Azure portal, click Marketplace.
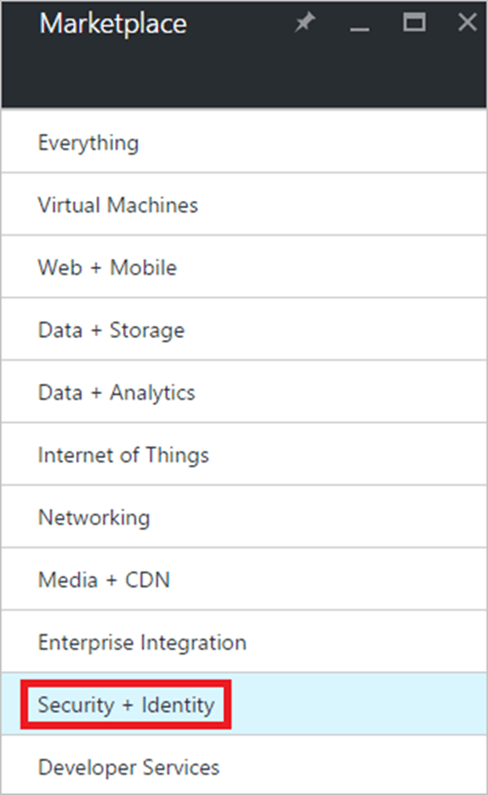
3. In the applications list, click Security + Identity.
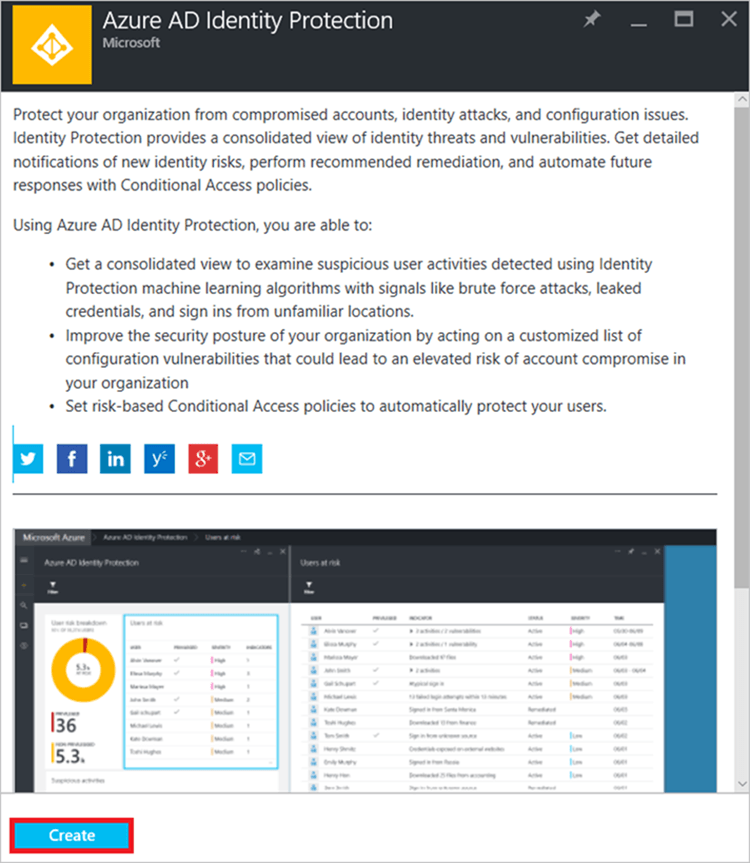
4. Click Azure AD Identity Protection.
5. On the Azure AD Identity Protectionblade, click Create.