The Need:
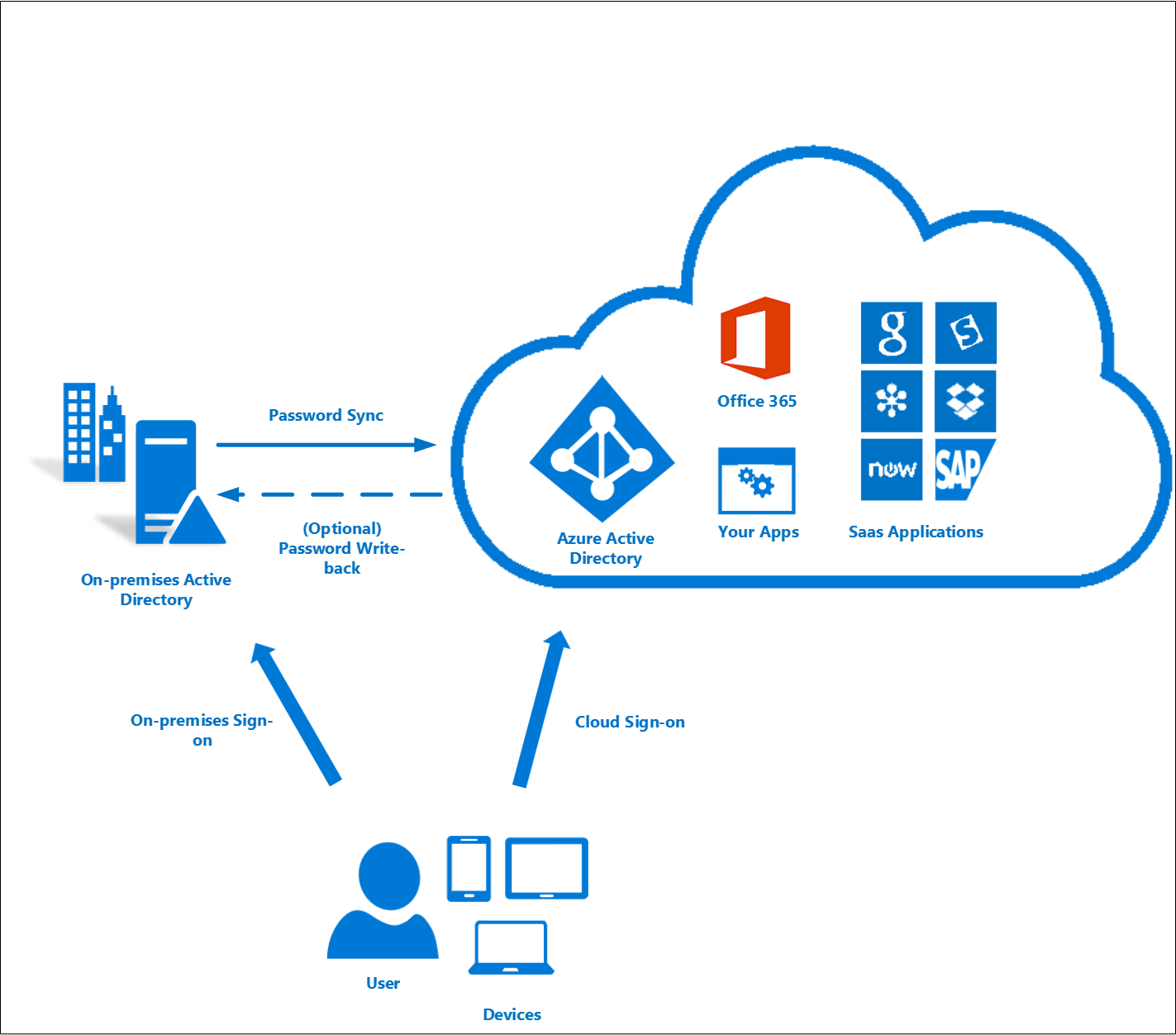
Password resets can often be burdensome for an organization’s help desk team, and being locked out of an account or device can leave users without access to their work at the most inconvenient times. Through Self-Service Password Reset (SSPR), integrated with Azure Active Directory, users in the office can easily regain access to their work in a secure manner, as needed. But did you know remote users (i.e. at home, onsite, off premise) can also regain access securely? This is accomplished through Azure AD without utilizing a VPN to connect to the organizations on-premise Active Directory. Remote users can reset their password via the Microsoft Cloud, which is then transcribed into Azure AD. Since the company is already utilizing Azure AD Connect, Azure AD can easily write the new password back to the local on-premise Active Directory. This feature not only relieves the burden from the organization’s help desk team, it also allows the user to regain access in a timely manner and return to work.
One of the largest problems surrounding SSPR is not the deployment of the services, but the user training surrounding it. With Windows 10 Build 1803, things just became a whole lot simpler in regards to the user training and process. I am going to first take you through the prerequisites for SSPR and then talk about how things have changed with Windows 10 April 2018 Update (Build 1803).
The Prerequisites:
There are a few Microsoft Services that are perquisites to SSPR if you are in a Hybrid Active Directory Environment utilizing Azure Active Directory Connect (AAD):
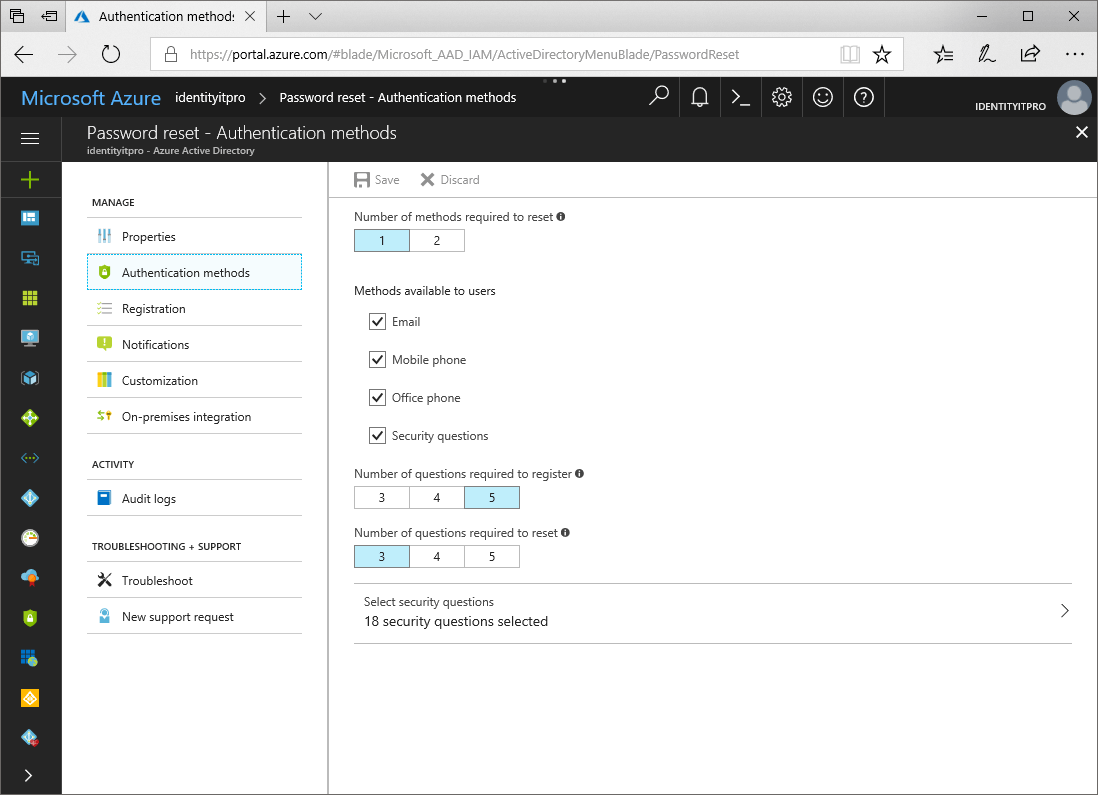
- Password Writeback must be setup and enabled within AAD Connect.
- Permissions within your local Active Directory must be setup with the AAD Connect Connector Account.
- Multi-Factor Authentication (MFA) should also be rolled out within your environment.
- Register your users for SSPR.
The User Experience
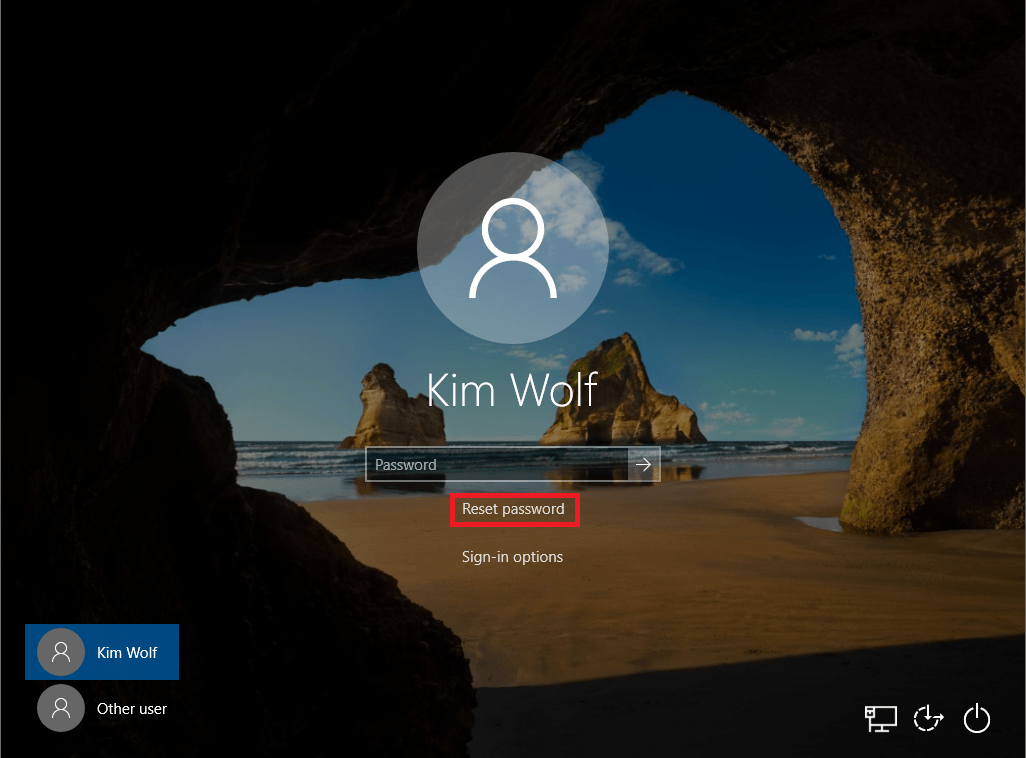
Once you have successfully deployed SSPR within your organization users normally have to visit https://passwordreset.microsoftonline.com/ in order to reset their password. The issue with this is users must have access to another device in order to access the website. When traveling or in other business predicaments, users may only have access to the device they are locked out of. This is where one of the new features within Windows 10 1803 saves the day! Utilizing Microsoft Intune a Mobile Device Management (MDM) platform, a part of the Microsoft EMS Suite, administrators are able to push out a policy enabling SSPR on the users Windows 10 Lock screen. Now that is pretty cool!
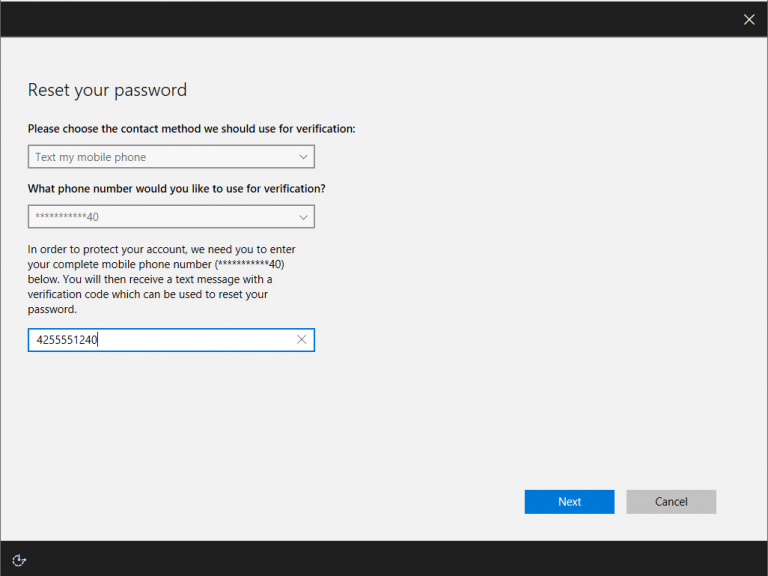
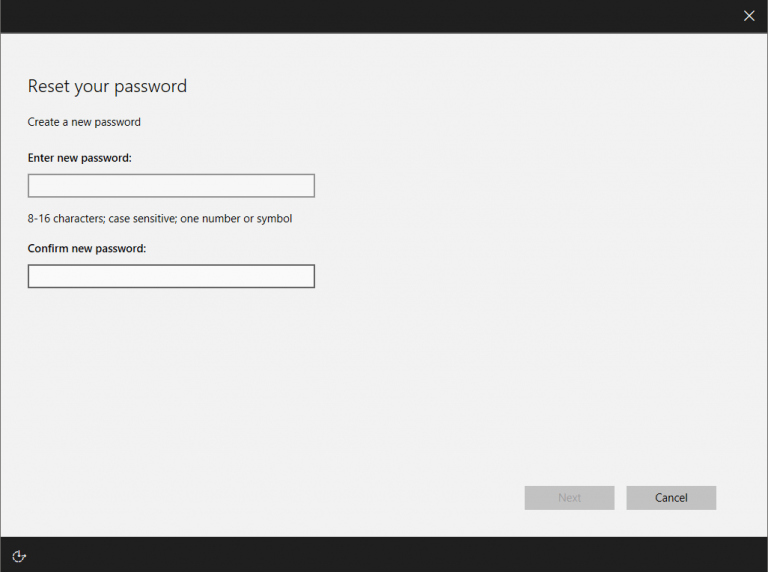
Once clicked, users will be taken through the SSPR process.
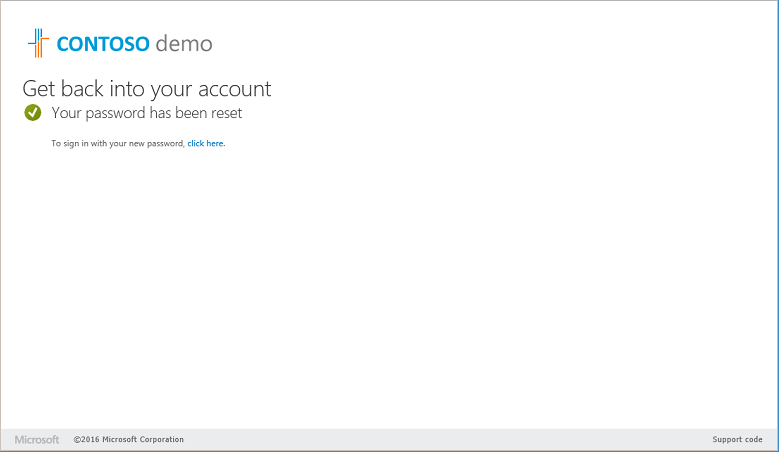
Once the process is completed, the password will be written back to your local Active Directory immediately and the user will be able to sign-in to the device they were once locked out of.
How do I enable this for my organization?
If you have already setup SSPR and your devices are Hybrid Azure AD joined or Azure AD joined, have a global admin configure an MDM policy, make sure your devices are running the latest version of Windows 10, and that’s it! Users will now see a “Reset password” link on their login screen.