In Part 4 of the "Phishing Attacks and Recommended Solutions to Protect Your Organization" webinar, we will review FortiMail’s Anti-Phishing solution and how Fortinet is able to able to protect your organization. We will be reviewing Platform Type, Requirements to implement, security measures such as FortiSandbox, Content Disarm & Reconstruction, Virus Outbreak Protection, Business Email Compromise, User Training, and other considerations. One important facet to consider with FortiMail is the power of the telemetry between other Fortinet products, which is referred to as the Security Fabric.
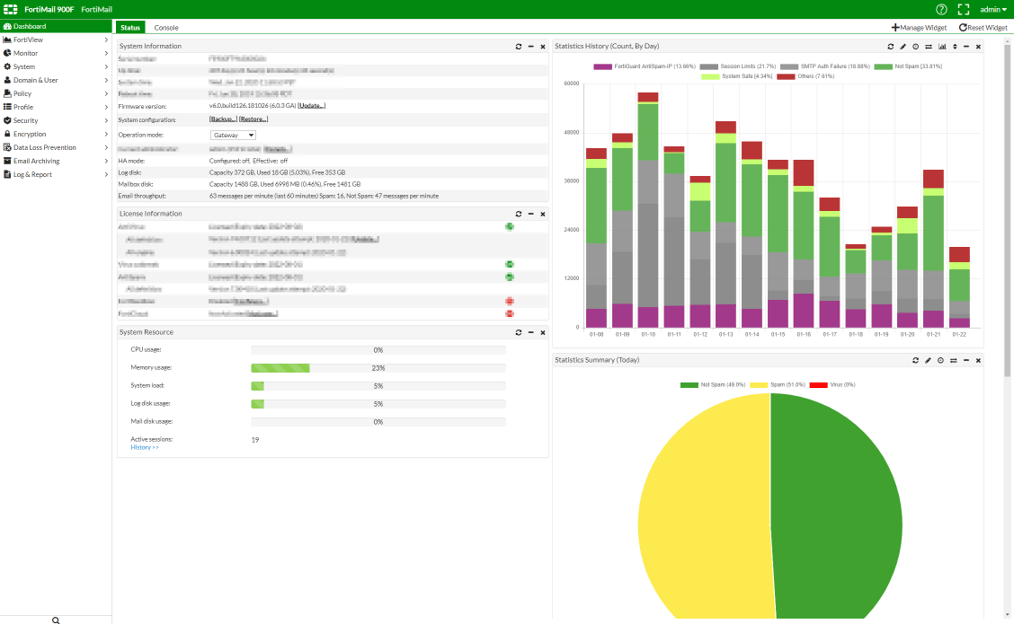
In the image below, you see the FortiMail web console, where you are provided a quick summary of various statistics as it relates to your email platform. FortiMail is one of the more unique solutions that is available on a platform level as an Appliance, Virtual Machine, or as a SaaS Solution. There is no requirements to implement and is available for all email platforms.
FORTISANDBOX
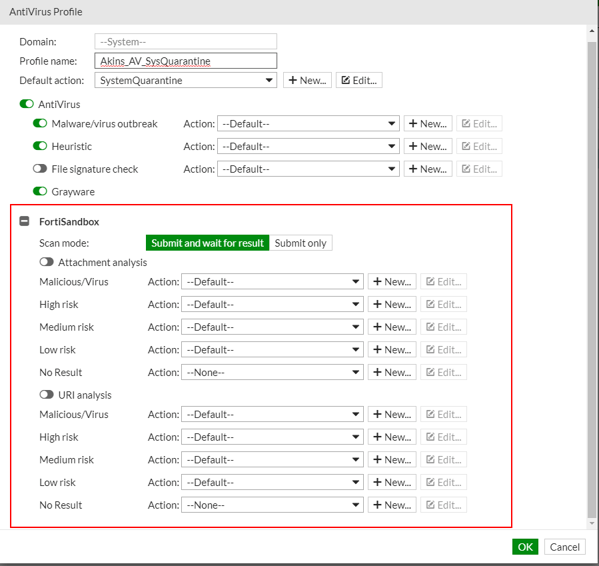
Moving into security measures, the first one we are reviewing here is FortiSandbox. This is Fortinet’s Zero-Day Threat Protection that provides AI based sandboxing to help combat previously unknown threats. FortiSandbox utilizes two machine learning models with static and dynamic analysis of suspicious objects. One consideration here is this is offered independently as an Appliance, Virtual Machine, or Saas Offering. Regardless of the platform selection, it delivers the same rapid detection and automated response and provides this information back to the Security Fabric.
VIRUS OUTBREAK PROTECTION
Moving into Virus Outbreak Protection (VOS), which you may have noticed earlier, can be configured with FortiSandbox. This AntiVirus policy closes the gap between antivirus updates and sandboxing, to detect and stop malware threats discovered between signature updates before they can spread throughout an organization. This services initiates a real-time look-up to our Fortinet's Global Threat Intelligence database, ensuring you will always have our very latest in malware protection.
In addition, here you see the granularity and control available to you to really fine tune this to your organizations needs.
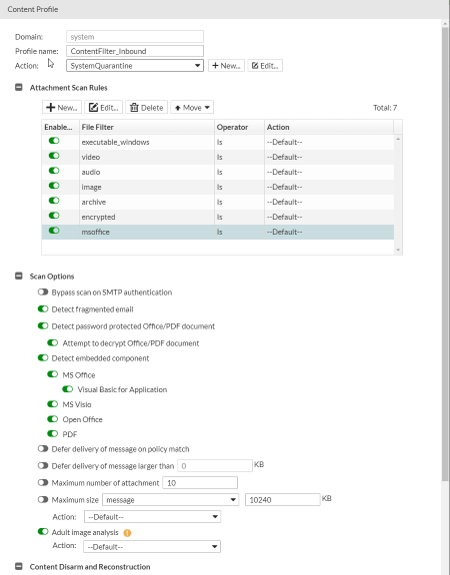
CONTENT DISARM & RECONSTRUCTION
Looking at Content Disarm & Reconstruction (CDR), we strip all active content from files in real-time, creating a flat sanitized file. All active content is treated as suspect and removed accordingly. Content Disarm and Reconstruction processes all incoming files, deconstructs them, and removes all elements that do not match firewall policies. CDR can fortify your zero-day file protection strategy by proactively removing any possibility of malicious content in your files.
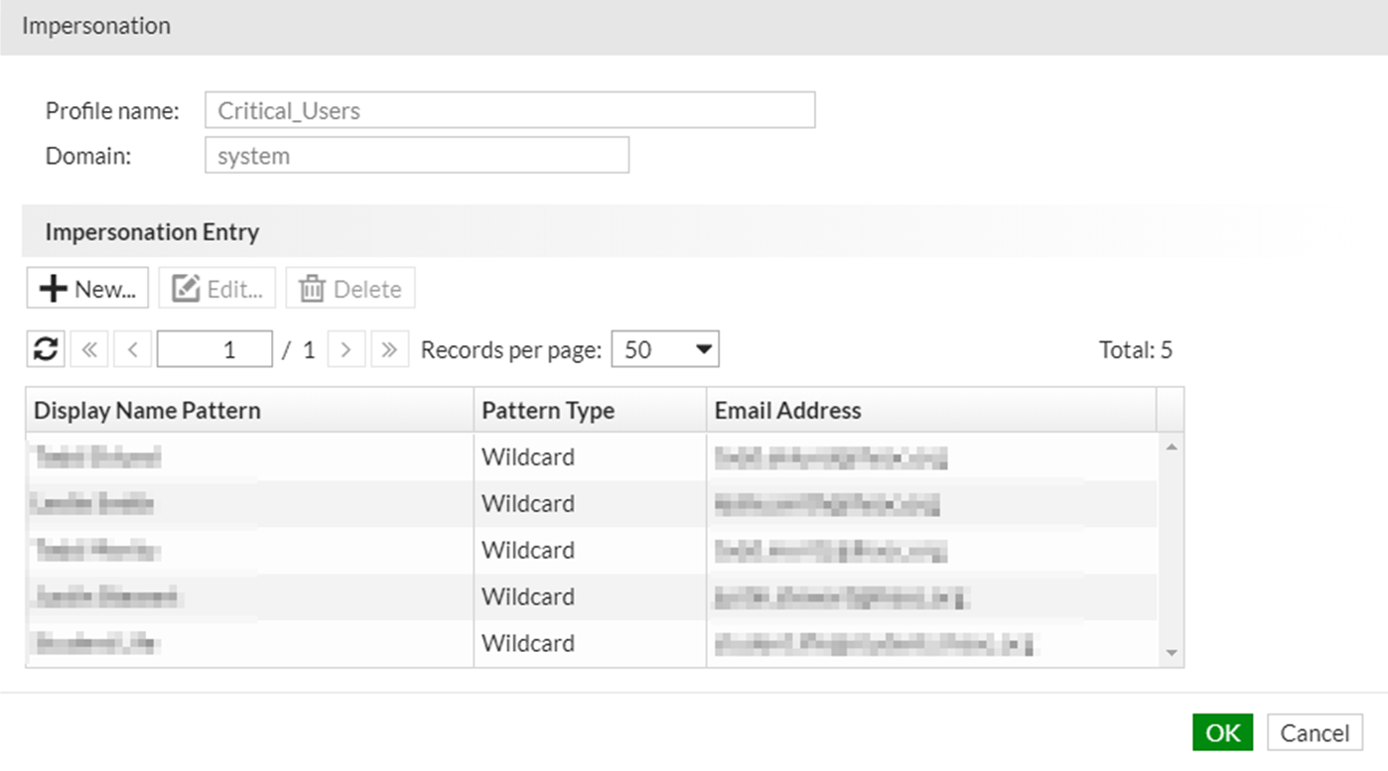
BUSINESS EMAIL COMPROMISE
Business Email Compromise (BEC) is FortiMail's solution to protect against email impersonation by mapping high valued target display names with correct email addresses. One key distinguisher here is that there are two types of mapping. Admins are provided the ability to manually enter this mappings or configure Dynamic Mapping– where the FortiMail Mail statistics Service can automatically learn the mappings. In addition to this, you are able to use these two types of mappings in tandem.
UNIFORM RESOURCE IDENTIFIED
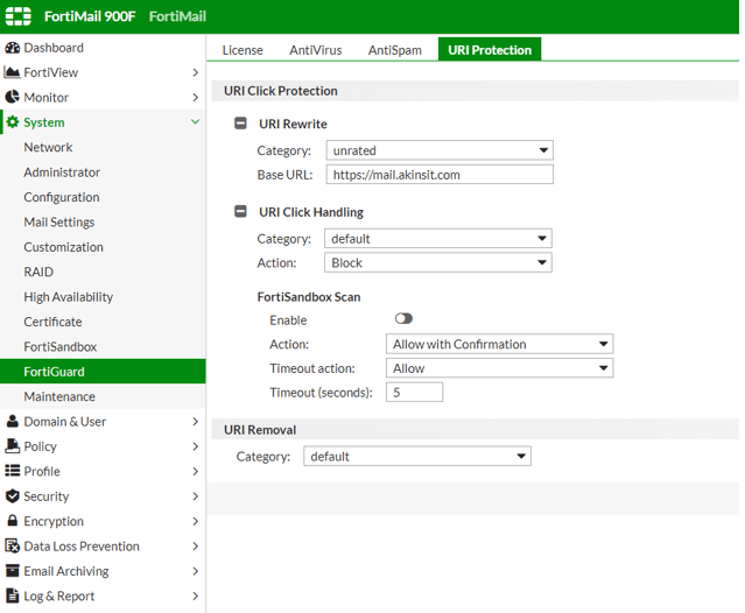
Similar to other solutions mentioned in the previous blogs on Mimecast and Office 365, we have URI Click Protection. Urls are rewritten in email message where they then will be directed to the FortiMail device for additional FortiGuard filtering. This can be configured to work in tandem with FortiSandbox for an additional inspection.
USER TRAINING
User Training is not as a strong of a focal point with the Fortinet Suite. While they have in-depth training available through their Network Security Expert Program– it is designed for technical professionals. With that being said, you are able to create a customizable disclaimer or replacement messages to generally warn recipients of the contents in emails. On the downside, these can become stale and repetitive and disregarded when users are over-saturated. While one could argue that this Fortimail solution is comprehensive enough to eliminate the need all together, it is one facet of security to consider– as it is ultimately your last layer of defense against phishing and unknown malware. If one was to consider Fortinet’s product, I would be inclined to compliment it with a solution such as KnowBe4.
OTHER CONSIDERATIONS
So in terms of Integration with Fortimail, we have Fortinet's own suite of products such as FortiGate, FortiWeb, FortiADC, FortiProxy, and FortiClient. There are also third-party solutions such as AtarLabs, Azure, Nutanix; all help organizations adopt a proactive approach to security by sharing Indicators of compromise across a seamless Security Fabric. While there are not as many third-party solutions directly with FortiMail, they do have an extensive list of partners that I would encourage you to check out when considering Fortinet’s ecosystem as a solution.
In addition to this, this solution does support LDAP (Lightweight Directory Access Protocol) and Single Sign On – which seamlessly allows end users into their Personal User portal.
ADVANTAGES
Some advantages of the FortiMail solution would be the telemetry with Fortinet's suite of products that provides Endpoint and device protection, application security, network security, and threat intelligence sharing, which really enhances the overall threat awareness and broadens threat response. In addition to this, they are more unique when it comes to the various platforms available and the sheer granularity with their policies. Lastly, they do provide user portals similarly to other solutions.
Some improvements that could be made would be email continuity , user training, and overall ease of use for new technical administrators.
CONCLUSION
If you found the above information valuable and would like to see how Fortinet can enhance your email security in your organization, contact us.